From the factory, Android security is relatively acceptable, although not the best. The system offers some protection against viruses, thefts, spies, hackers, interventions and practically any similar threat.
Let’s see how Android security is in this regard and what specific functions this system brings to protect itself against this type of thing.
Contents
How to protect my cell phone from viruses
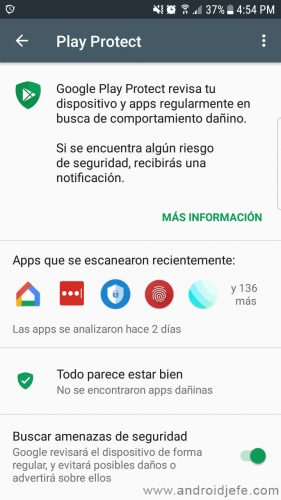
Certified Android devices have a powerful application called Google Play Services. This includes an antivirus system that is responsible for frequently scanning the applications that you install on your device. If it finds any APK or suspicious app, it will notify you.
To protect your cell phone from viruses, it is best to install applications from the Play Store only. The reason is that there the applications are analyzed by Google. But in case of installing a downloaded APK anywhere else, Google Play Services will notify you if it detects that the installed APK is malware or some type of malicious app that is a threat. That is, this security verifies all the apps installed on your Android, regardless of where you have obtained them.
It is for this reason that Google has stated that it is not necessary to install an antivirus if you download from Google Play (although you should not trust this). A type of antivirus is already installed on the system thanks to Google Play Services. This security is part of what the company calls Google Play Protect (android.com/play-protect/)
You can verify that the virus analysis of your installed applications is activated in the Settings of the Android system. Select “Google” and on the next screen tap on the “Security” option. Tap Google Play Protect and you can see all the information about it. On this screen, verify that the ” Search for security threats ” option is activated.
On the other hand, Google Play Protect also recommends using Google Chrome. The reason is that this browser has a security system that alerts you when you enter malicious web pages. It is a good idea to use this browser to visit the Internet.
How to protect my cell phone from spies or interventions
Basically, for someone to spy on you or intervene on your phone, they should have installed an application with these capabilities. But if so, Google Play Protect will probably notify you of it.
Beyond that, we can only assume that Android offers the necessary security for reliable communication. But in any case, you must consider that no system is perfect. If you are looking for absolute security, personal communication would be best. Regarding instant messaging, one of the most recommended security applications is Signal or Telegram.
Protect Android from Hackers 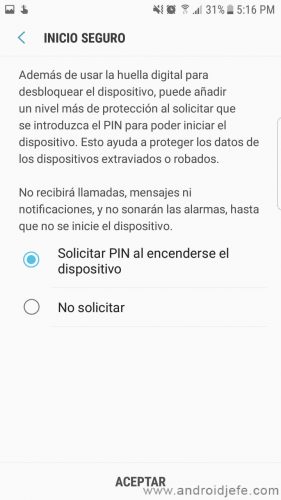
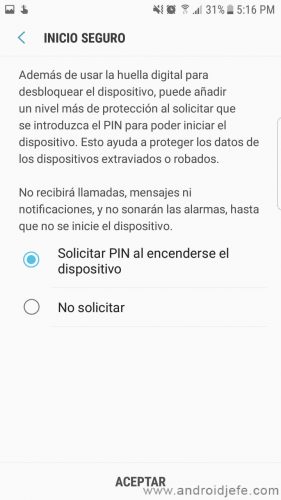
As long as you’re afraid of the data stored on your phone, an easy way to protect it is to encrypt the device with a pin or password. In this way, only you can unlock the device with that key and see your data every time you turn it on. Without that key to unlock the mobile, it is difficult for a hacker to obtain that information, even if he has the equipment in his possession.
You can even protect and encrypt the data on your memory card. Android offers this option in your system settings, “Security” option.
Modern Android devices no longer even require encryption of the device. You only have to configure the password request when turning on the phone, as can be seen in the image above. You can find it in Settings> Security.
How to protect my cell phone from theft
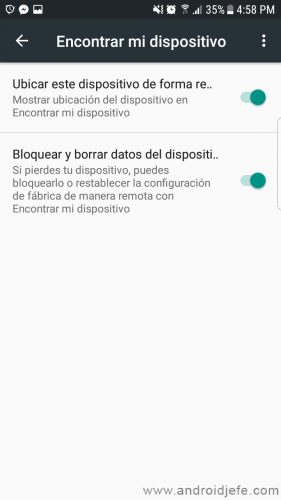
Another important security in the Android system, thanks to Google, is the one that allows you to protect your cell phone from theft. Not literally, but it can help you know the location of your stolen device. Even in case you can’t recover it, you can erase the data from the device remotely.
Similarly, this feature is activated by default in the Android system. If you want to make sure of it, see the Android system settings. Choose the option “Google” and there choose “Security”. Tap the “Find my device” option.
In case your device has been stolen, you must enter the website google.com/android/find from another computer, using the Google account registered on your cell phone. There you can determine the location of the equipment as well as make it ring or delete the data. You can view more information here.
Another anti-theft security on Android is the so-called Factory Reset Protection or Device Protection. It prevents the phone from being used after an unauthorized reset. If the data of the equipment is restored other than the mobile settings, the data of the owner’s Google account will have to be entered so that the phone can be used again. This feature is available on devices with Android 5.1 or higher.


Cerberus web platform
If you want to improve this functionality, you could consider buying an app like Cerberus, which offers much more complex and advanced options for anti-theft protection. For example you can obtain the location of the equipment, erase the data and more actions remotely using SMS commands. This avoids the need for the phone to be connected to the Internet, an important requirement in the case of the Google function mentioned above.
Android security applications?
We would like to say that you do not need to install any security application for Android. Unfortunately, when it comes to viruses, it doesn’t. On previous occasions, Google has had to remove malware from its Google Play store, which has been downloaded hundreds of thousands of times.
Despite what has been said, we cannot recommend keeping an antivirus app permanently installed on Android. The problem is that most of these apps tend to slow down your phone and quickly drain the battery. Some even have invasive advertising. If you think that your mobile has viruses or malware, scan the device with a trusted antivirus and then uninstall. If it’s about scanning files, use Virus Total.
Security on Android mobile devices
Android, like any other operating system, is not perfect and can be vulnerable now or later. Despite that, it offers acceptable native security options, which allow you to protect your computer against various situations or basic threats. At least for the conventional user, this is already very good.
Receive updates: SUBSCRIBE by email and join 10,000+ readers. Follow this blog on Facebook and Twitter.